
The AI-Native Protection Platform Powering Modern Security Operations
Traditional SIEMs weren’t built for AI-driven threats. Artemis closes that gap by dramatically reducing MTTD and MTTR, stopping attacks before they can cause adverse impact.
Trusted by top companies’ security teams all over the world
Security leaders trust Artemis
Traditional Tooling isn’t Effective Enough.
The era of AI is quickly accelerating this.
One Size Doesn’t Fit Any
Generic detections fall short and require highly manual investigation
Ingest Pricing Limits Visibility
Rigid ingestion architecture prevents analysis of all necessary context and telemetry (and cost a lot)
Threat Intel at Human Speed
Going from intel report to detection takes weeks. Attackers move in hours.
Continuous Protection with AI Woven in Every Layer
As an AI-native protection layer, Artemis reliably detects and responds to important threats with actionable context, effortlessly.
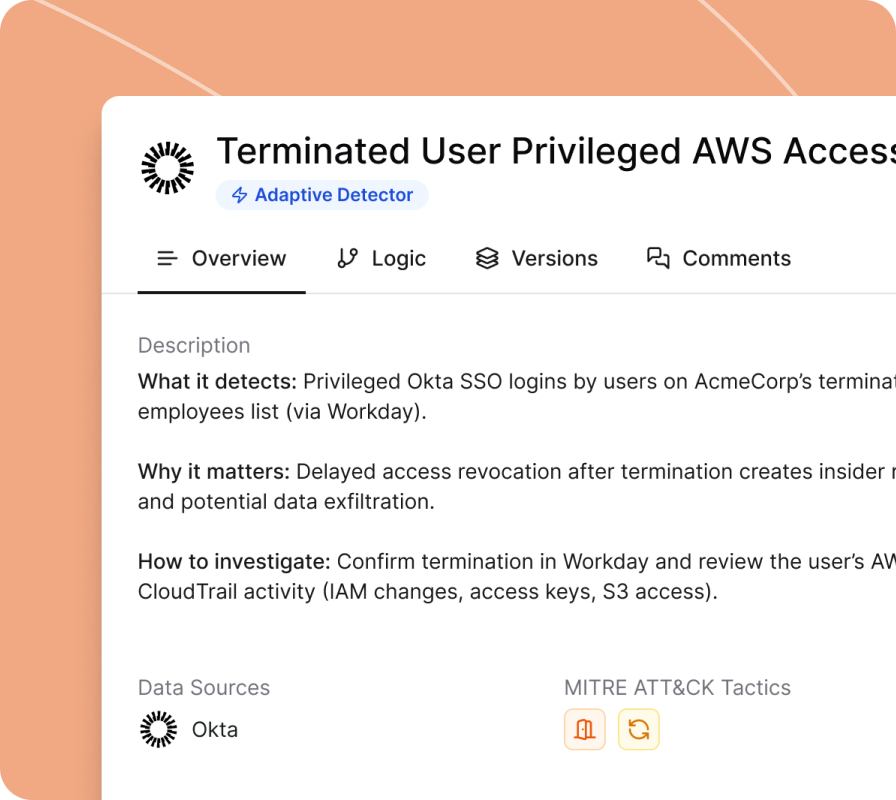
Detections that adapt to your environment
Artemis learns your technical and business environment, continuously creating and fine-tuning detections specific to you - acting as your AI Detection Engineer
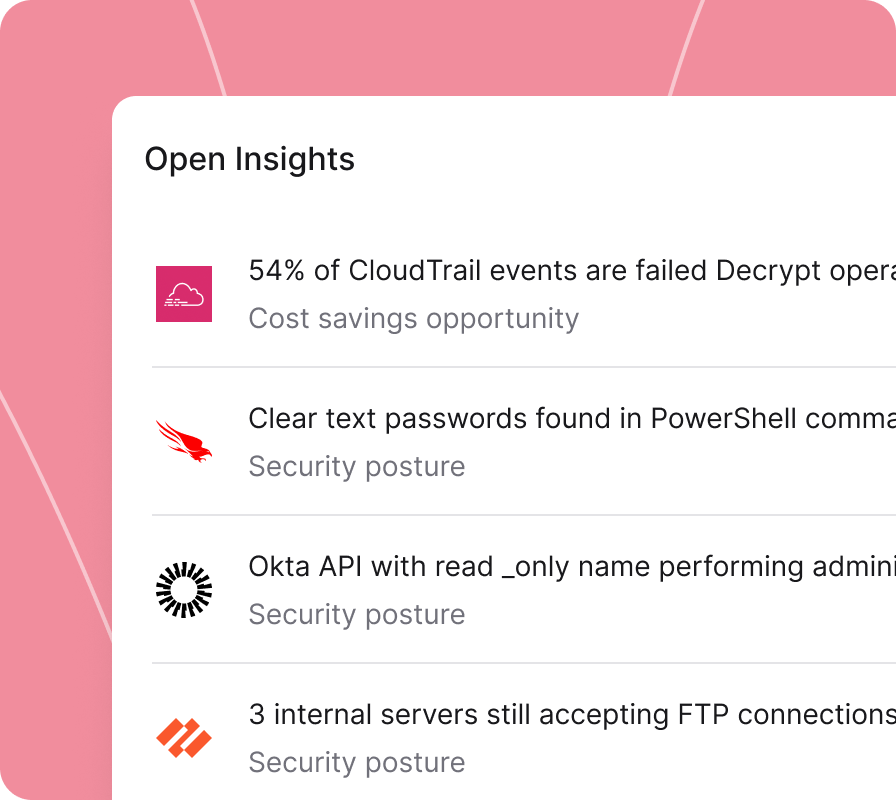
Environment intelligence
Artemis analyzes identity, cloud, endpoint, and network telemetry to highlight security posture hygiene issues, cost savings opportunities, and shadow AI usage. Insights are tailored to your environment - not generic benchmarks
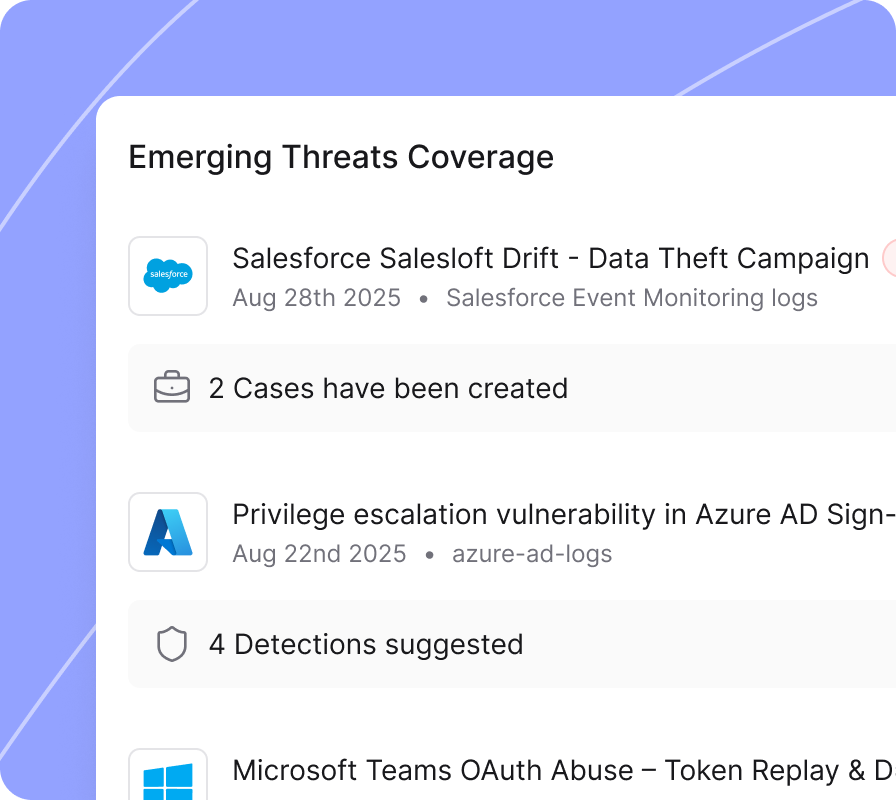
Threat intel at machine speed
AI analyzes emerging threat intelligence and automatically closes detection gaps for new exploits - acting as your AI Threat Intel Analyst
Give Your Team
Superpowers with AI
Most "AI" in security is a chatbot bolted onto legacy systems. Artemis agents act- empowering your team to write detections, investigate your environment, and close gaps within minutes instead of days.
Drop a threat report and Artemis will map it to MITRE ATT&CK, check your coverage, and write environment-specific detections based on your assets - ready for review, not research.
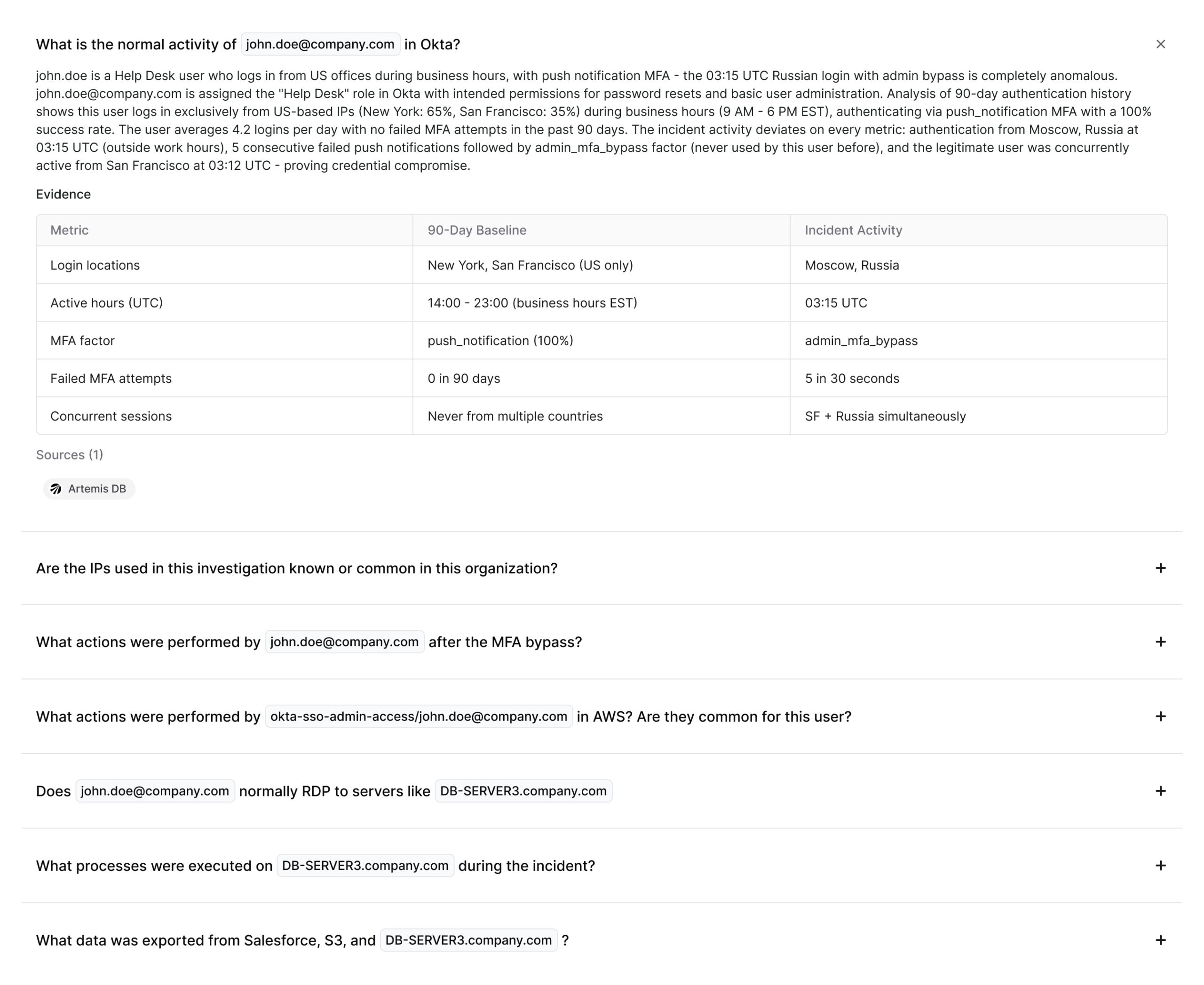
Traditional threat hunting requires days of manual work. With Artemis, you simply ask and agents investigate autonomously across your entire environment - asking follow-up questions, correlating evidence, and delivering actionable report your team can act on.
No query syntax to learn. No filters to configure. Ask what you need to know in natural language and get a direct, analytical answer - not a raw table of results.
Threat Intelligence
& Incident Readiness
Know your coverage. Close your security gaps. Reduce costs. Stay ahead of emerging threats.
Stop guessing about coverage. Artemis maps your telemetry against attack patterns and shows exactly where you're blind across Cloud, Identity, Network, and SaaS.
A single view of what's happening across your environment - open cases, metrics, SLAs, and security score - so you spend your time acting, not assembling the picture yourself.
Artemis continuously surfaces insights on security posture, cost, and shadow IT improvements opportunity by building a living model of your assets, users, configurations, and business context.
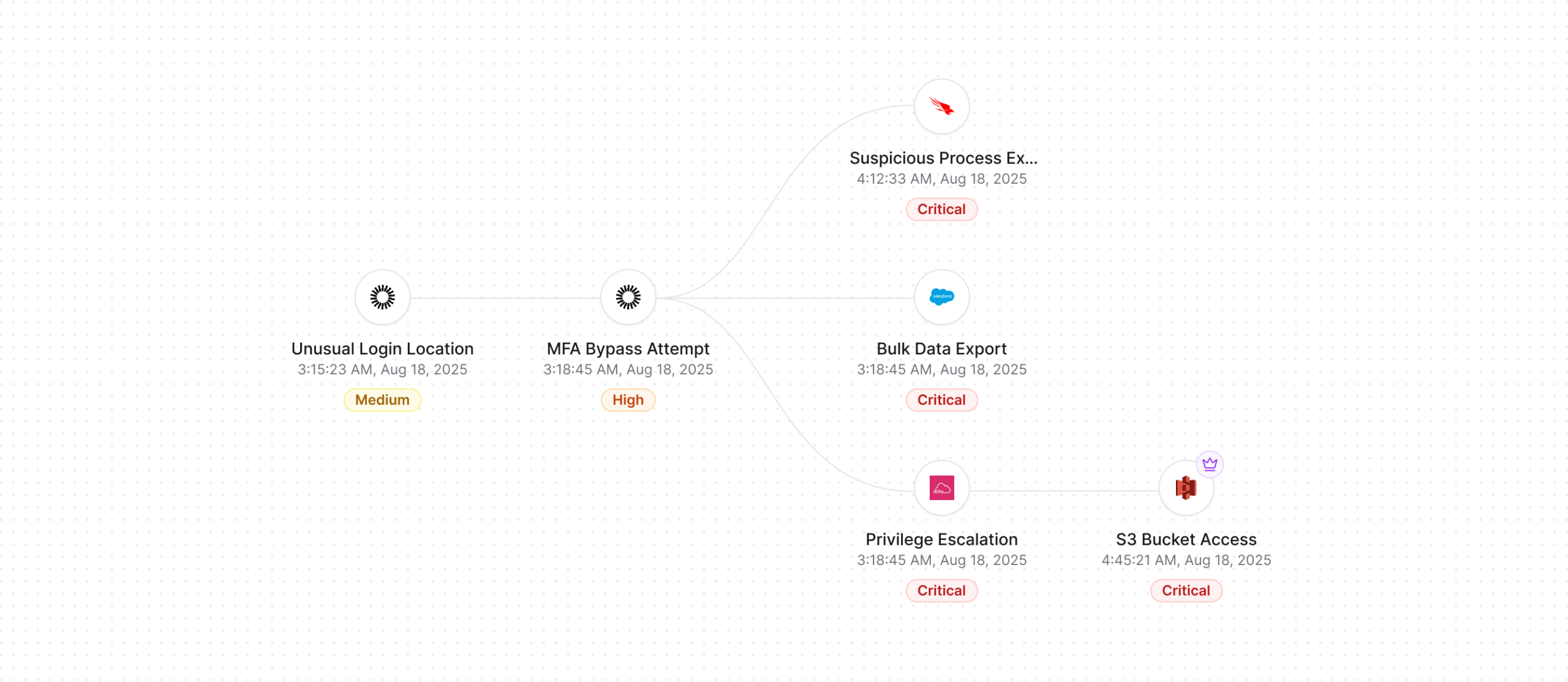
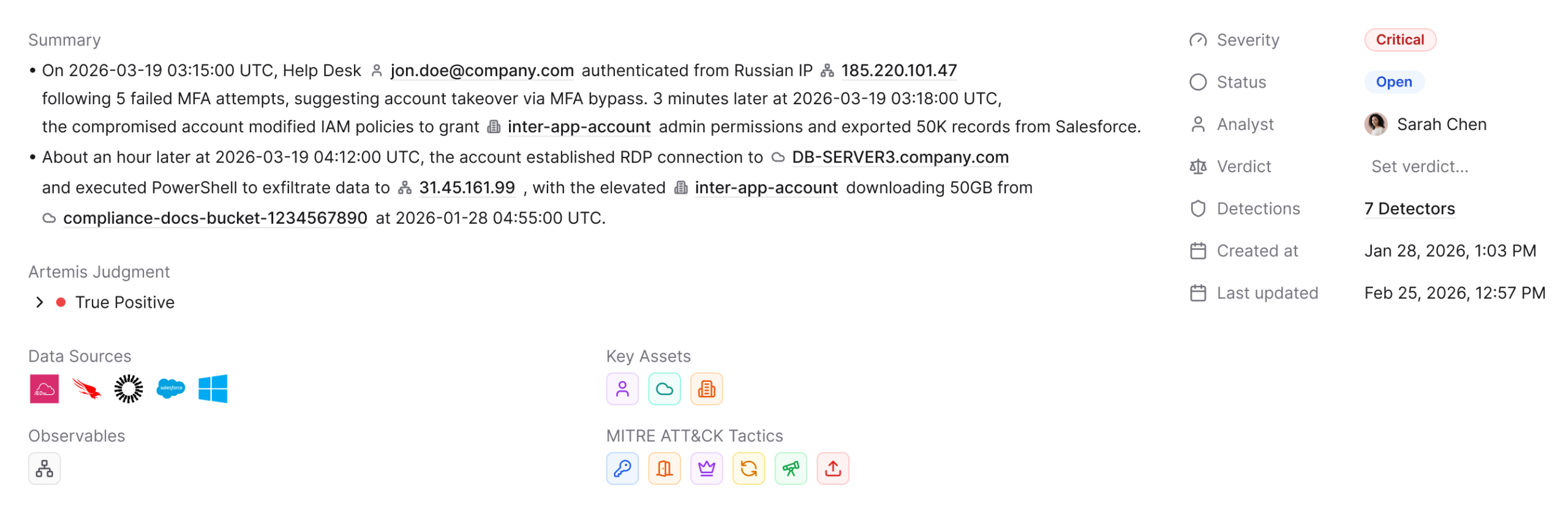
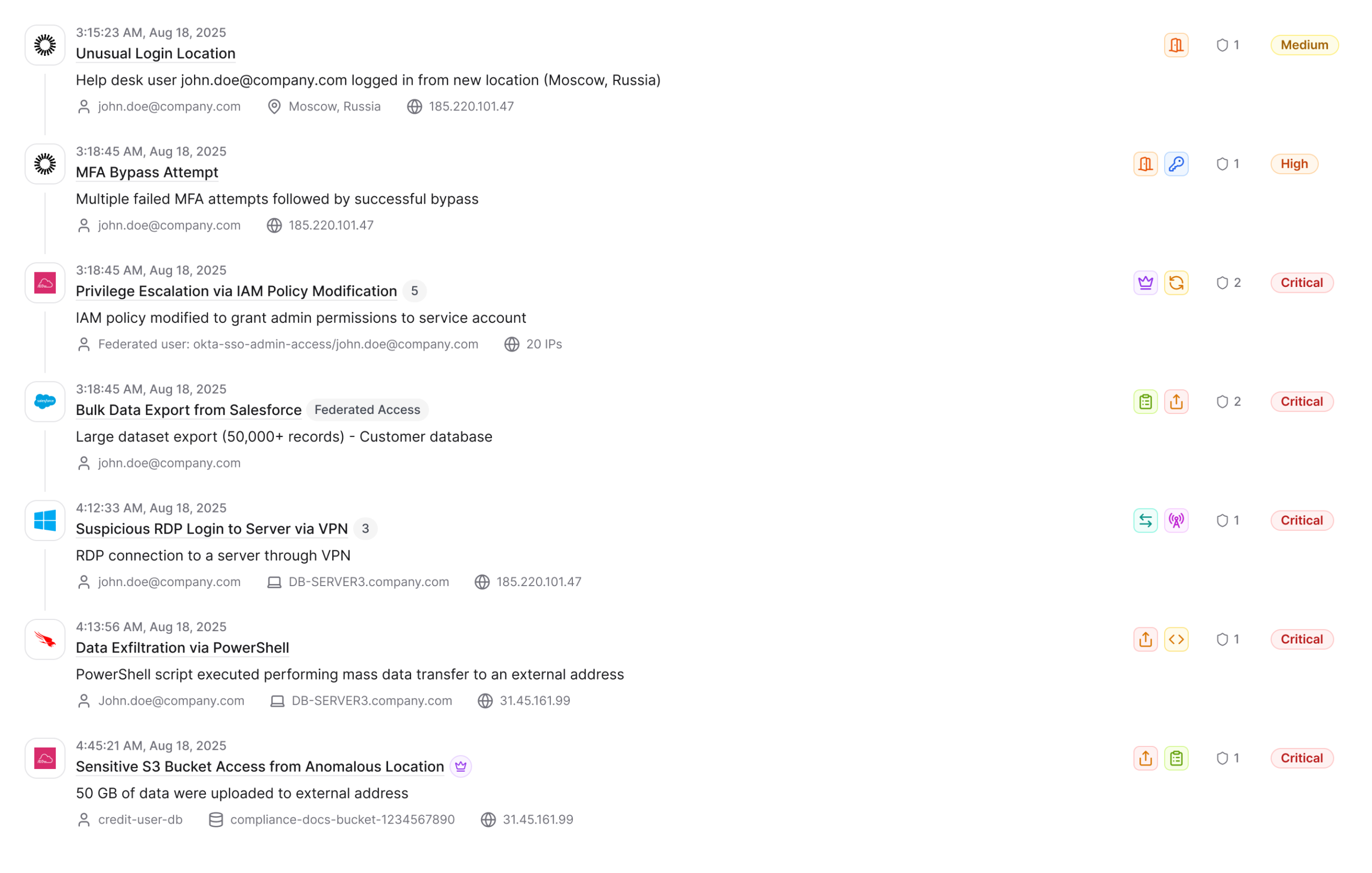
Full Attack Stories, Not Isolated Alerts
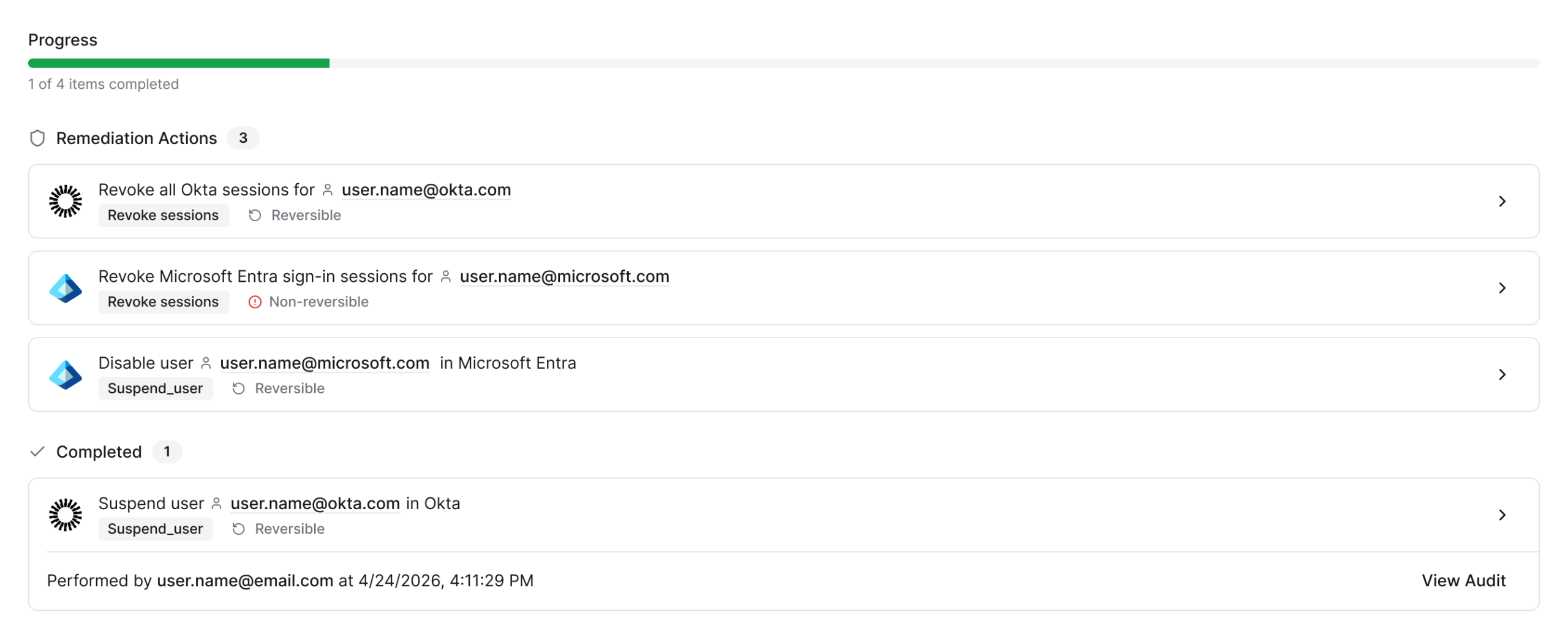
From first signal to final response - Artemis help you handle the entire attack chain. It detects threats, enriches them with context, investigates autonomously by correlating activity across every log source, and delivers a complete case with response actions. Then, you pick it up at the decision point.
Case Summary
Artemis vs Legacy SecOps Tools
Most security vendors bolt AI onto legacy architecture. Artemis was built AI-native from the ground up. It can augment your existing SIEM or replace it.
| Artemis | Legacy SecOps Tooling | |
|---|---|---|
| Environmental context | Continuously maps relationships between users, AI agents, assets, behaviors, org structure, and business context. Artemis understands your organization. | Tools don't understand your environment, your business, your org structure, or your risk priorities. Every alert lands cold. |
| Time to value | Minutes. Connect a source, get environment-specific detections and insights immediately. | Months of deployment, professional services, rule tuning. |
| Detection quality | Detections continuously generated and tuned to your environment. Correlates across identity, cloud, endpoint, network, SaaS. Detects multi-stage, multi-domain attacks single-source tools miss entirely. | Thousands of generic rules. Most don't apply. Tune forever or ignore. Each tool sees its own slice. Multi-stage, multi-domain attacks spanning identity, cloud, and endpoint go undetected. |
| Mean time to resolution | 96% reduction in mean time to resolution. Artemis covers the full lifecycle - detection, correlation, investigation, response, and containment. You have the choice on what you want Artemis to do on your behalf. | Detection without action. Your team bridges the gap between alert and containment with hours of manual investigation, Slack threads, and ticket queues. |
| AI Mode | Ask your security data questions in plain English. Create detections, investigate, explore data - through conversation, not code. Any analyst, any skill level. | Investigating means writing SPL, KQL, or SQL. AI assistants bolted on top of legacy query engines still require you to think in the tool's language. |
| Threat intel response | Drop a report in or subscribe to feed. Coverage gaps closed automatically within minutes. | Read report, map TTPs, write rules, test. 2 weeks to coverage. |
Artemis
Continuously maps relationships between users, AI agents, assets, behaviors, org structure, and business context. Artemis understands your organization.
Legacy SecOps Tooling
Tools don't understand your environment, your business, your org structure, or your risk priorities. Every alert lands cold.
Artemis
Minutes. Connect a source, get environment-specific detections and insights immediately.
Legacy SecOps Tooling
Months of deployment, professional services, rule tuning.
Artemis
Detections continuously generated and tuned to your environment. Correlates across identity, cloud, endpoint, network, SaaS. Detects multi-stage, multi-domain attacks single-source tools miss entirely.
Legacy SecOps Tooling
Thousands of generic rules. Most don't apply. Tune forever or ignore. Each tool sees its own slice. Multi-stage, multi-domain attacks spanning identity, cloud, and endpoint go undetected.
Artemis
96% reduction in mean time to resolution. Artemis covers the full lifecycle - detection, correlation, investigation, response, and containment. You have the choice on what you want Artemis to do on your behalf.
Legacy SecOps Tooling
Detection without action. Your team bridges the gap between alert and containment with hours of manual investigation, Slack threads, and ticket queues.
Artemis
Ask your security data questions in plain English. Create detections, investigate, explore data - through conversation, not code. Any analyst, any skill level.
Legacy SecOps Tooling
Investigating means writing SPL, KQL, or SQL. AI assistants bolted on top of legacy query engines still require you to think in the tool's language.
Artemis
Drop a report in or subscribe to feed. Coverage gaps closed automatically within minutes.
Legacy SecOps Tooling
Read report, map TTPs, write rules, test. 2 weeks to coverage.













